The BSI has issued a warning level of orange, which means: “The IT threat situation is business-critical. Massive disruption to regular operations.” The trigger is once again the disastrous security situation of Microsoft Exchange – the most important communications center for many companies, organizations and authorities. The BSI sees the administrators who are responsible for the misery as not implementing the known and urgently needed security precautions; However, there is no critical word towards Microsoft in the current BSI warning.
Advertisement
In the wake of the Hafnium gaps, the BSI declared a red warning level in 2021 when almost all Exchange servers were hijacked and provided with backdoors. The situation is currently not quite as dramatic. But the BSI still sees at least 17,000 servers in Germany alone – which corresponds to 37 percent of all accessible systems – as “highly at risk”. In fact, “over half of all Exchange servers in Germany are probably vulnerable to critical vulnerabilities.”
The spread and importance of Exchange makes this a real problem: “Many schools and universities, clinics, doctor's practices, nursing services and other medical facilities, lawyers and tax advisors, local governments and medium-sized companies are particularly affected,” explains the BSI. And they are threatened with danger from all directions, including “the encryption of data with subsequent blackmail and ransom demands.”
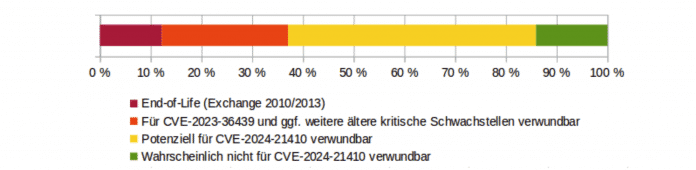
Red is definitely vulnerable, yellow means: “You don't know for sure.” But according to the BSI, well over 50 percent of all servers are probably vulnerable to critical vulnerabilities.
(Image: BSI)
The root of evil
The basic problem is Exchange versions that are no longer supported by Microsoft (2010, 2013 with at least 12%), which no longer receive updates and therefore have several known and critical security gaps. They are basically wide open; The BSI classifies the operation as “high risk”. There are also current versions that do not have the latest patches (25%) and therefore also have known security gaps (e.g. CVE-2023-36439).
And then there are the servers where you can't tell from the outside, without specifically attacking them, whether all the necessary security measures, such as activating extended protection, have been taken – and that's almost half. Here, the BSI rightly assumes that a significant proportion are vulnerable to attacks. This means that probably over half of all Exchange servers are vulnerable to attacks. Only a meager 15 percent of servers are running the latest version Exchange 2019 CU14, in which Microsoft activates the extended protection required for secure operation, so they probably no longer have any known vulnerabilities.
Create a remedy
As urgently necessary countermeasures, the BSI calls for discontinued Exchange versions to be scrapped, all patches or cumulative update packages – the so-called CUs – to be installed and, of course, extended protection to be activated. The associated BSI warning that thousands of Microsoft Exchange servers in Germany remain vulnerable to critical vulnerabilities is aimed at the operators of Microsoft Exchange servers and their administrators.
They can tell you a whole lot about how difficult and time-consuming it is to keep an Exchange server up to date and therefore secure. And that the manufacturer Microsoft is often no help, but rather part of the problem. Because he would actually much rather sell you a cloud subscription with annual fees. That meant letting Microsoft run its own communications center entirely, which isn't a particularly attractive option for many given privacy concerns and Microsoft's own security record.
Given the disastrous security record of Microsoft Exchange, one could of course also place the cause and responsibility for the problem with the Exchange product or its manufacturer, Microsoft. One could give arguments and suggestions for improving the situation in this direction, or perhaps even suggest and promote safer alternatives. The BSI says nothing about this.
By the way: In our exclusive expert forum from heise Security Pro (membership required), IT security and data protection managers from companies, authorities and companies discuss the technical aspects of secure IT operations as well as possibilities where and how you can avoid Microsoft's quasi-monopoly can escape. Well-founded and practical-oriented, without any flat-out “this wouldn’t have happened with Linux”. You can find out more about heise Security Pro here:
(yeah)



