Metadata is extremely important when analyzing and further processing security gaps. In addition to the severity level, which is given a value between 0 and 10 in the CVSS methodology (Common Vulnerability Scoring System), machine-readable information about affected products and versions, the type and exploitability of the vulnerability and the patch status are also important.
Advertisement
Manufacturers of security products for threat prevention and logging, such as firewalls, SIEM (Security Incident and Event Management) and XDR (Extended Detection and Response), rely on being able to quickly access the enriched vulnerability data in order to be able to react to new threats.
The NVD (National Vulnerability Database), a US government organization and part of the NIST standards authority, is responsible for enriching the CVE data. However, she has no longer taken on this task since mid-February; Since then, there has been a notice on the NVD's homepage about “delayed analysis efforts”.
Reporting makes you free? The NVD informs about delays and asks users to be patient
(Bild: Screenshot / heise security)
The fact that the analysis and enrichment of security gaps is merely delayed is a very glossed over fact. Of over 2,200 CVE ID vulnerabilities published since February 15, only 59 have metadata attached and 2,152 are unused. Since dozens to hundreds of new gaps are added to the CVE list every day, it will be difficult to catch up with the backlog.
After all, the CVSS assessment is often carried out by those reporting a security vulnerability themselves, so that this information is available for many CVEs despite the work interruption at the NVD.
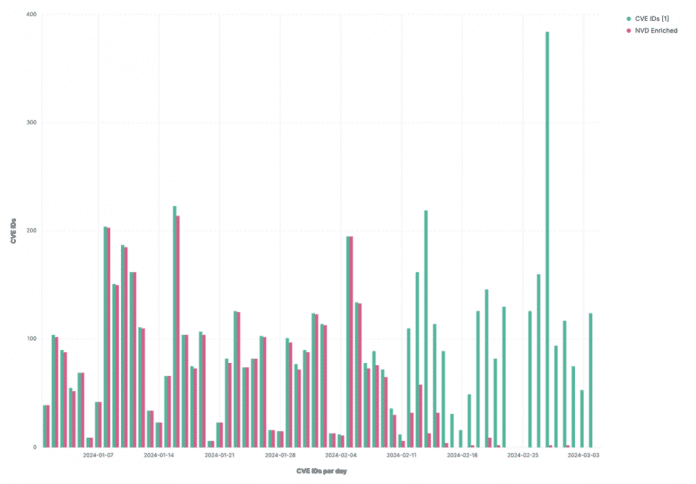
The NVD has only enriched a few CVE IDs with metadata since mid-February.
(Image: Anchore)
The NVD is currently keeping quiet about how it plans to deal with the thousands of open security gaps and, above all, when it will resume its work.
NVD compulsory for US federal authorities
This situation is particularly annoying for companies that want to sell their IT security products to the US government. According to the latest version of the FedRAMP (Federal Risk and Authorization Management Program) guidelines, providers must use NVD data to describe security gaps – for example in vulnerability scans. Spicy: NIST, administrator of the national vulnerability database, is involved in the creation of the FedRAMP guidelines.
The CVE system is currently under increasing criticism. cURL developer Daniel Stenberg has repeatedly criticized the allocation practice, and the database is bursting at the seams: Over 25,000 new CVE IDs were allocated in 2023, an increase of 15 percent compared to the previous year.
(cku)



