More than a month after a critical vulnerability in FortiOS and FortiProxy was discovered, over 100,000 vulnerable devices are still online. This was the result of an updated evaluation of the “Shadowserver Project”. The data from the internet-wide monitoring project shows that admins worldwide are still too hesitant to patch – so there has been only minimal improvement since the count began on March 6th.
Advertisement
As of yesterday, March 10, 145,795 Ivanti devices were still vulnerable on the Internet using CVE-2024-21762, 2,446 of which were in Germany. The United States remains the hardest hit, with over 24,000 vulnerable devices.
A graphic on the project website illustrates the slow spread of patches that have been available since February. This is surprising, as the flaw in the SSL VPN of Ivanti devices is a critical, remotely exploitable vulnerability that allows code smuggling and achieves a CVSS score of 9.6. Providing a quick remedy – even by temporarily switching off the SSL VPN – should be high on the task list of conscientious network administrators.
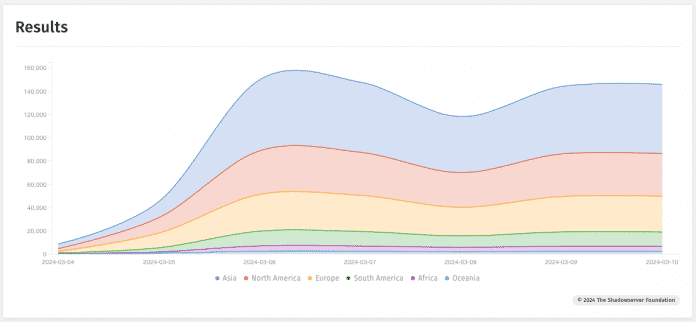
Little movement: Forti admins are apparently hesitant to patch. The sharp increase from March 5th is due to a changed measurement method.
(Bild: The Shadowserver Foundation / Screenshot: heise Security)
CISA: Attack on Ivanti devices
Meanwhile, the US cybersecurity agency CISA had problems with products from another manufacturer in February: According to media reports, attackers attacked two of the agency's Ivanti VPN gateways, which then immediately took the devices offline. However, the exact extent of the attack remains unclear, as CISA neither commented on its homepage nor answered questions about the incident.
CISA issued an emergency directive in February that included a shutdown order for certain vulnerable Ivanti products. CISA orders are binding for US federal authorities.
(cku)



