Google warns of three security holes in the Chrome web browser. The developers close them with updated software. Users should install the update quickly, as with this risk assessment the vulnerabilities can usually be abused to inject malicious code by visiting carefully prepared websites.
Advertisement
As usual, Google does not provide any more detailed information in the version announcement. At least the programmers provide brief information about all three gaps. The most serious brings the reporter a $12,000 reward. This is a possible access outside the intended memory limits in the Javascript engine V8 (CVE-2024-2173, no CVSS value, Google risk rating “hoch“).
Google Chrome with three high-risk leaks
Google's developers only describe another vulnerability in the V8 engine as an “inappropriate implementation”, but they do not explain what it consists of (CVE-2024-2174, no CVSS value, hoch). The discoverer receives a reward of at least 7,000 US dollars. The anonymous submitter who reported a use-after-free vulnerability in the FedCM component (Federated Credential Management, used for single sign-on systems) will receive $6,000 (CVE-2024-2176, no CVSS value, hoch).
The updated versions of the Chrome web browser are now Chrome 122.0.6261.105 for Android, 122.0.6261.111 for Linux and 122.0.6261.111/.112 for macOS and Windows. The long-term stable version has also been updated by the manufacturer; the version 122.0.6261.112 is now considered current for Mac and Windows.
Current status?
You can find out whether the web browser is already running in a new version in the version dialog. It opens by clicking on the symbol with the three stacked dots to the right of the address bar and then under “Help” – “About Google Chrome”. This displays the currently running version and starts the update process if an update is available.
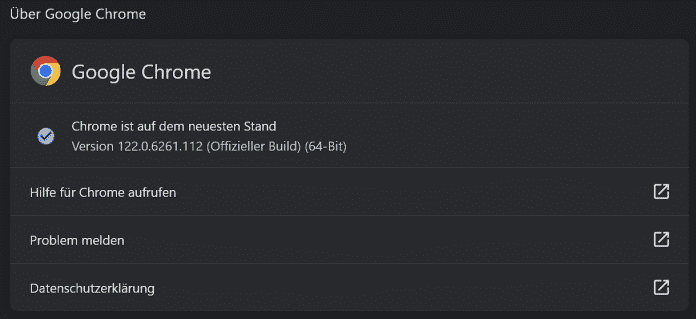
The version dialog starts the update process if necessary.
(Bild: Screenshot / dmk)
If you use Chrome under Linux, you start the distribution's software management. Since the security gaps also affect other web browsers based on the Chromium project, such as Microsoft's Edge, new versions that can be installed in similar ways are likely to be available soon.
Last week, Google's programmers had already patched four vulnerabilities in Chrome. They classified at least two of them as high risk.
(dmk)



