Mozilla Foundation programmers have plugged two critical security holes in the Firefox web browser and one in Firefox ESR. Users of these browsers should apply the update quickly.
Advertisement
The security advisory for Firefox 124.0.1 lists two critical security vulnerabilities that the new version seals. Attackers could read or write a Javascript object outside the intended memory limits. This is supposed to be a deception of a so-called “Range-based bounds check elimination” mechanism (CVE-2024-29943, no CVSS, risk according to Mozilla “critical“) have been successful. Basically, this involves checking whether memory limits are being adhered to.
Firefox: Two critical security vulnerabilities
The second critical vulnerability also affects Javascript. Attackers were able to inject an event handler into a privileged object and thus execute arbitrary Javascript code in the parent process with high privileges (CVE-2024-29944, no CVSS, critical). This gap only affects the desktop versions of the web browsers, but in addition to Firefox 124.0 and older versions, it also affects Firefox ESR 115.9 and older. Although the security notices do not describe what attacks would actually look like, viewing carefully prepared websites is usually enough to abuse these vulnerabilities.
Only the security fixes can be found as changes in the release notes for Firefox 124.0.1. Mozilla browser users should apply the updates quickly. The easiest way to do this is to use the version dialog, which opens by clicking on the symbol with the three horizontal lines to the right of the address bar and continuing via “Help” – “About Firefox”.
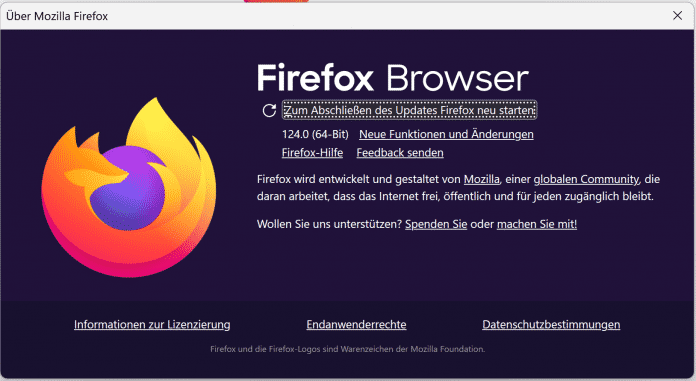
The Firefox version dialog shows the currently running software version, starts the update if necessary and at the end asks you to restart the browser.
(Bild: Screenshot / dmk)
Since Thunderbird has not yet received an update, the vulnerability in the Firefox ESR code base on which Thunderbird is based is apparently not exploitable – Javascript is not executed by default in emails. It was only on Tuesday that the Mozilla Foundation released the updates to Firefox 124.0, Firefox ESR 115.9 and Thunderbird 115.9 as planned. The developers have also closed several security gaps, but these achieved the maximum risk rating of “high”.
(dmk)



