The “electronic patient file for everyone” should come from mid-January 2025, provided there has been no objection beforehand. While some fear becoming transparent patients, for others it is not quick and easy enough – doctors and pharmacists criticized the planned implementation of the ePA. With the digital strategy for the healthcare system, the ePA should finally get off the ground and deliver added value and data, if the Federal Ministry of Health has its way.
Advertisement
The relationship of trust between doctor and patient is also crucial in the projects. If the patient has the feeling that the doctor handles the information in a trustworthy manner, then, according to Sebastian Zilch, sub-department manager for gematics, e-health and telematics infrastructure at the Federal Ministry of Health, patients are more willing to provide the doctor with data for the examination.
In order to conduct research with the data stored in the telematics infrastructure – the health network – work was carried out in parallel on the Health Data Use Act. This is intended to enable the flow of data into the planned health data room.
Initially, it should be possible to retrieve the e-prescription from the electronic patient record (ePA) – still in the opt-in version – in July of this year. This emerges from a “roadmap” that Zilch presented at an event organized by the North Rhine Association of Statutory Health Insurance Physicians on the future of the ePA.
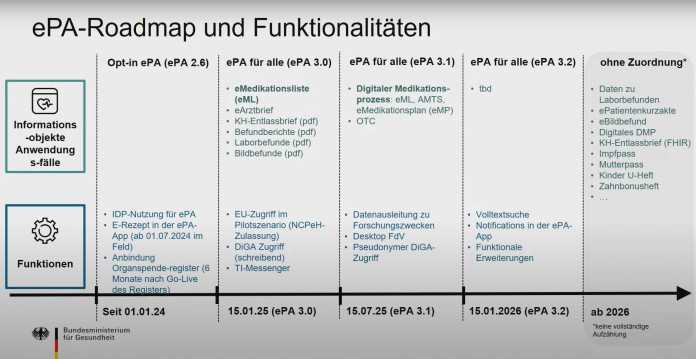
Roadmap of the Federal Ministry of Health for the electronic patient file (2024 to 2026).
(Image: BMG)
The wishes and reality of those involved sometimes differ somewhat. “It's too late to cook when you're supposed to apply,” says the managing director of the Federal Association of Health IT (bvitg), Melanie Wendling, commenting on the Federal Ministry of Health's ambitious plans. According to Wendling, the years missed in advancing the digitalization of the healthcare system cannot be made up in such a short time.
“Fast food instead of star cuisine”
According to Wendling, “open and honest communication in all directions” is part of the digitalization projects. “As we all know, the devil is often in the details and errors only become apparent in real operation,” says the bfitg boss. It should therefore not be expected that the ePA will function smoothly by mid-2025. At the same time, the interim managing director of Gematik, Florian Hartge, promises in an interview with the Ärztezeitung that the patient files planned for next year should come “without additional mouse clicks”. For Wendling, on the other hand, it is important that “the right expectations” are created so that “there is no disappointment if you suddenly find yourself in a fast food restaurant instead of a starred kitchen.”
The court is clear, but according to Wendling, important ingredients are left out; a slimmed-down version of the ePA will initially be released in 2025. Doctors and psychotherapists fear that filling out the ePA will mean even more duties and bureaucracy for doctors. They would also like to have an electronic medication plan and a functioning full-text search within the ePA at the beginning of 2025, but these are planned for 2026.
Full-text search planned for 2026
According to Prof. Dominique Schröder from the Chair of Applied Cryptography at the Friedrich-Alexander University Erlangen-Nuremberg, however, a full-text search within the ePA is not necessary because unimportant function words are not searched for anyway: “Therefore, the use of encryption technologies that… enable a search within the encryption. This technology is called 'Searchable Encryption' and ensures that encrypted data can be searched for predetermined keywords, such as a specific disease. Searchable Encryption has been researched in cryptography for over 20 years and is already in used in practice, for example in the MongoDB database. Amazon AWS also offers such approaches that enable searches. “These techniques are not only state of the art, but also state of the art,” says Schröder.
Level of protection in VAU can be high
Another point of criticism is that the data in the ePA, which is loaded into a trusted execution environment (VAU) for processing, is not additionally encrypted there. From the perspective of Thomas Eisenbart, Professor of IT Security at the University of Lübeck, the level of security in a VAU can be “very high if the implementation of the VAU and the entire system takes into account the current status of attacks and patches and the infrastructure is kept up to date.” . Since the technology has only been on the market for a few years, the threat situation is constantly changing, said Eisenbarth. “This means that at the moment active work on the infrastructure is essential in order to achieve high security goals. Then the decryption within the VAU should be considered appropriate by design.”
Central data storage
It is also criticized that, as before, the data is collected centrally and in the future, with the ePA for everyone, even more data will be stored at the Health Research Data Center. The specifications and the security concept are not yet ready. The Chaos Computer Club, for example, criticized in an open letter that “in the discussion about the Health Data Usage Act and central patient data collections, there is often the unfounded threat that meaningful knowledge can only be generated by accessing real data.”
And Prof. Esfandiar Mohammadi, head of the Privacy & Security working group at the University of Lübeck, also sees this as a possible risk: “Central data storage leads to a single point of failure: attacking parties can invest all their resources in it, “To compromise this one point. This includes both technical attacks and the compromise of employees. In systems that are distributed over a large area, attacking parties have to divide their resources.”
When asked, Gematik said that it generally proceeds methodically in its security analysis: “The methodology is based on the relevant procedures of the BSI, for example, establishing protection requirements, risk analysis and also the consideration of threats,” said a Gematik spokesman. Gematik also carries out “regular and event-related audits of the operators of TI services”. An independent security assessor would also be used for the ePA filing systems. In addition, the operators of TI services are integrated into TI's information security management system. This allows “continuous monitoring of security by Gematik”. Incidents could therefore be identified quickly.
Virus scanners as a security risk
Another point of criticism of the ePA is that a central virus scanner is not provided. According to Gematik, the virus scanner could endanger security because it would have to communicate with systems outside the protected environment. “To ensure IT security, the systems used in the supply must also provide appropriate virus protection programs,” says Gematik. According to Eisenbarth, a virus scanner in the VAU represents an additional security risk. Instead, the code in the VAU should be kept as simple as possible and checked for vulnerabilities using verification procedures and code auditing.
(mack)



